Cyberattacks are rising as companies adopt distributed computing, remote working, the cloud, and open-source software. Gartner reveals that 68 percent of organizations experienced at least one ransomware attack in 2021 — 65 percent experienced more than three, and 15 percent experienced 10 or more attacks.
Security must be at the heart of software development to make safe, resilient applications. Threat modeling, automated security alerts, and streamlined incident responses are integral components, and DevSecOps tools are instrumental. By blending development, security, and operations, these tools support efficiency and bolster your security posture by automating security processes.
Assessing the many DevSecOps tools on the market, including open-source and free DevSecOps tools, would take quite some time. Fortunately, we’ve already done the hard work, reviewing numerous tools for DevSecOps and whittling them down to the 13 best.
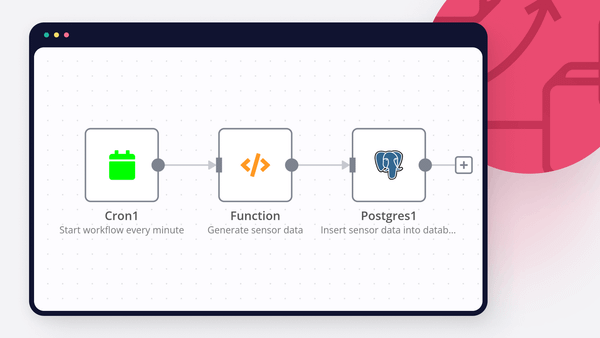
We’ll also show you how to use n8n’s workflow automation software to quickly integrate these tools into other DevSecOps tech stacks and services, extending their functions with a seamless workflow.
Here is our list of 13 best DevSecOps tools
- MISP (Malware Information Sharing Platform)
- TheHive
- Cortex
- SIGNL4
- Rundeck
- PagerDuty
- Sentry.io
- ServiceNow
- SecurityScorecard
- Microsoft Graph Security API
- Elastic Security
- Grafana
- Splunk
13 best DevSecOps tools list — Reviewed with industry expertise
Packed with features like monitoring, alerting, threat data visualization, and automation, the following tools can dramatically improve your security posture. All of them integrate with n8n, so adding them to your development workflows is straightforward.
1. MISP
(Free)
The Malware Information Sharing Platform (MISP) is a threat intelligence platform for sharing, storing, and correlating indicators of compromise (IoC) from different attacks.
MISP is open-source and free to download and use. However, both the MISP Project and third-party businesses offer support and training for commercial use.
Key features:
- An efficient IoC and indicators database — This feature stores both technical and non-technical information about incidents and attackers, along with malware samples. It provides a standardized format for describing threats, making it easier for teams and analysts to understand and act on the data.
- Built-in sharing functionality — MISP supports seamless collaboration by synchronizing events and attributes. Its filtering capabilities simplify compliance with information-sharing policies.
- An intuitive user interface (UI) — This makes it easy for teams to create, update, and collaborate on events and IoCs.
| Pros of MISP | Cons of MISP |
|---|---|
|
|
2. TheHive
(Paid and free options)
TheHive is an incident response platform that’s tightly integrated with MISP. It enables DevSecOps teams to investigate MISP events, collaborate in real-time on events, and triage events based on severity.
TheHive has three pricing tiers:
- Community (free)
- Gold (starts at $21,500 annually)
- Platinum (starts at $28,000 annually)
Key features:
- Alert management — TheHive has a dedicated alert page where teams can leave comments, define custom alert statuses, escalate alerts, and identify similar alerts.
- Case management — Teams can create cases for different security events, set metrics and observables (like an IP, URL, or file) to track, and document the incident response process using TheHive’s built-in template engine.
- Metrics and dashboards — Teams can compile and correlate case statistics, observables, tasks, metrics, and more to create key performance indicators (KPIs) and track security progress over time.
| Pros of TheHive | Cons of TheHive |
|---|---|
|
|
3. Cortex
(Free)
Cortex originates from the same parent organization as TheHive. It features an observable analysis mechanism that helps teams collect and analyze observables, respond to threats, and interact with other teams. With Cortex, teams can query tens or hundreds of observables from a single tool, streamlining workflows.
Cortex is freely available as open-source software under the Affero General Public License (AGPL).
Key features:
- Automated analysis — Cortex helps automate the security data analysis. It integrates with various security tools and services, automatically processing indicators of compromise (IOCs), malware samples, and other security data.
- Customizable analyzers and responders — Users have the flexibility to create custom analyzers and responders tailored to their specific needs.
- Integration with TheHive — This integration streamlines the incident response workflow by allowing the automatic execution of analyzers and responders from within TheHive. It promotes an efficient and well-orchestrated incident response process, enhancing security.
| Pros of Cortex | Cons of Cortex |
|---|---|
|
|
4. SIGNL4
(Paid)
SIGNL4, a cloud-based mobile alerting solution crafted by Derdack, automatically notifies relevant team members about critical events through their mobile phones. Using targeted, persistent texts, phone calls, and push notifications, SIGNL4 alerts active staff on duty to help track and escalate incidents.
SIGNL4 is a paid tool offering four pricing packages:
- Starter (free, but pay per text or call)
- Notify & Connect ($9 per user/month)
- Optimize ($15-19 per user/month)
- Maximize ($25-29 per user/month).
Key features:
- A mobile app — SIGNL4 is a lightweight, easy-to-use mobile app supporting push notifications, not just texts and calls.
- Required acknowledgment — The app continues to send alerts until they’re acknowledged. If it doesn’t receive a response within a set timeframe, it initiates an automated multi-tier escalation process.
- A keyword-based filter — SIGNL4 uses a keyword-based filter algorithm to ensure only necessary alerts are passed, reducing the likelihood of “alert fatigue” among staff.
| Pros of SIGNL4 | Cons of SIGNL4 |
|---|---|
|
|
5. Rundeck
(Free with paid version)
Rundeck is a runbook automation tool for business continuity, self-service operations, and incident management. Teams can use Rundeck to execute different jobs across tools, scripts, APIs, and system commands.
Rundeck is a free, open-source project. However, PagerDuty also offers a paid version called Rundeck Enterprise, which includes enterprise-ready distribution of Rundeck, additional capabilities, and access to support from the Rundeck team. For pricing, contact the PagerDuty team.
Key features:
- Logging and auditing — Rundeck provides detailed audit logs and reporting to support compliance and security monitoring. Teams can refer to these logs to determine who carried out specific actions, helping them investigate security incidents and meet regulatory requirements.
- Access control and security — Rundeck offers robust access control mechanisms, allowing DevSecOps teams to define who can perform specific tasks and access sensitive systems and data. This is crucial for enforcing security policies and ensuring that only authorized personnel can execute security-related operations.
- Self-service portals — Organizations can configure Rundeck to provide self-service portals, enabling teams to independently initiate security scans, compliance checks, and other security-related tasks.
| Pros of Rundeck | Cons of Rundeck |
|---|---|
|
|
6. PagerDuty
(Paid with free option)
PagerDuty, the parent company of Rundeck, specializes in cloud computing for IT department incident response services. Tailored for critical operations, PagerDuty lets teams orchestrate, automate, and accelerate incident response across their infrastructure.
PagerDuty offers four pricing packages:
- Free (a pared-back version)
- Professional ($21 per user/month)
- Business ($41 per user/month)
- Digital Operations (contact PagerDuty for pricing).
Key features:
- Response automation — Teams can use a low or no-code builder to create automation pipelines that contact responders, inform stakeholders, send status updates, and more.
- IT service management (ITSM) integration — PagerDuty integrates with hundreds of tools, including popular ITSM tools like ServiceNow, BMC Helix, and Jira Software, to track and resolve tickets.
- Central job orchestration — PagerDuty allows teams to establish standardized automatic jobs across select (or all) relevant environments from a singular, secure connection.
| Pros of PagerDuty | Cons of PagerDuty |
|---|---|
|
|
7. Sentry
(Paid with free option)
Sentry is a tool that helps teams monitor and fix crashes in real-time. It aids in diagnosing code-related issues and optimizing code performance. With an approachable UI and visualization capabilities, Sentry streamlines the troubleshooting process, allowing teams to rectify errors before they impact users.
Sentry has four pricing packages:
- Developer (a pared-back free option)
- Team ($26/ month)
- Business ($80/month)
- Enterprise (request a demo to learn more about pricing for this plan)
Key features:
- Visual replay — The session replay feature lets teams replay every step of the user’s session before and after encountering an issue. This visual replay facilitates identifying the timing and root of the problem, leading to faster remediation.
- Distributed tracing — This feature offers an end-to-end visual overview of API calls and database queries. Teams can perform a distributed trace to locate poor-performing API calls, latency-ridden database queries, and any related errors.
- Version change highlighting — Sentry’s Releases feature distinguishes between resolved and newly introduced errors, making it easier to sort through version changes.
| Pros of Sentry | Cons of Sentry |
|---|---|
|
|
8. ServiceNow
(Paid)
ServiceNow, a cloud computing platform, helps organizations manage business services, incidents, user roles, and more. With extensive automation capabilities, it expedites incident response. ServiceNow’s customizable workflows enable teams to define, orchestrate, and automate security and compliance checks across the software development lifecycle.
Get in touch with the ServiceNow team for pricing information.
Key features:
- Security incident response — This feature provides a structured framework for identifying, assessing, and responding to security incidents. It ensures that teams address security incidents promptly, reducing the risk of security breaches in DevSecOps environments.
- Governance, risk, and compliance — This module helps manage and track compliance with regulatory standards, security policies, and industry best practices. DevSecOps teams can use it to assess and mitigate risks throughout the software development lifecycle, ensuring security and compliance from the outset.
- Customizable automation workflows — ServiceNow’s powerful orchestration and automation capabilities allow DevSecOps teams to create custom workflows automating security and compliance checks.
| Pros of ServiceNow | Cons of ServiceNow |
|---|---|
|
|
9. SecurityScorecard
(Paid with free option)
SecurityScorecard, a risk management tool, aids organizations in maintaining and providing regulatory compliance. Besides generating compliance reports, the SecurityScorecard platform offers a holistic view of your security posture by assigning security ratings to components.
SecurityScorecard features three pricing tiers (exact pricing unavailable online):
- Free
- Business
- Enterprise
Key features:
- Security ratings — SecurityScorecard provides security ratings for your organization and third-party vendors, drawing on various cybersecurity risk factors. This rating system offers insights into the security of your systems, aiding decisions on vendor collaboration.
- Continuous monitoring — SecurityScorecard offers ongoing monitoring of an organization’s or vendor’s security posture. Teams can use this information to promptly identify and respond to security issues, integrating security into their development and operational processes.
- Issue prioritization — The tool identifies security issues and prioritizes them based on severity and potential impact.
| Pros of SecurityScorecard | Cons of SecurityScorecard |
|---|---|
|
|
10. Microsoft Graph security API
(Free but may require additional paid services)
The Microsoft Graph security API allows users to connect with various Microsoft security products, partners, and services. Its unified interface and schema streamline security operations, enabling teams to query all relevant Microsoft security providers and aggregate the results.
The Microsoft Graph security API is free to use but may require paid subscriptions for Microsoft and the third-party solutions it integrates with.
Key features:
- Real-time threat detection and alerting — The interface provides real-time access to security signals and threat intelligence data from Microsoft 365 services like Azure Active Directory, Office 365, and Windows Defender. DevSecOps teams can use these signals to proactively detect and respond to security threats.
- Pipeline integration — The Microsoft Graph security API easily integrates into continuous integration and continuous delivery (CI/CD) processes, enabling automated security checks and validation throughout the development lifecycle.
- Threat intelligence capabilities — The Microsoft Graph security API provides access to threat intelligence data, including IoCs, threat actor information, and security incident details.
| Pros of the Microsoft Graph security API | Cons of the Microsoft Graph security API |
|---|---|
|
|
11. Elastic Security
(Paid)
Elastic Security helps teams detect, respond to, and prevent security threats. With Elastic Security, teams can perform threat hunting, investigate and respond to security issues, and implement automated threat protection.
Elasticsearch offers four pricing tiers, each granting access to the Elastic Stack:
- Standard (starting at $95/month)
- Gold (starting at $109/month)
- Platinum (starting at $125/month)
- Enterprise (starting at $175/month)
Refer to the Elastic Security price estimator for more detailed pricing information.
Key features:
- Endpoint security — This enables teams to detect, respond to, and collect endpoint-related security issues from a central interface. It’s a particularly useful tool for preventing and mitigating malware and ransomware attacks.
- Security and information and event management (SIEM) capabilities — This allows DevSecOps teams to detect and respond to threats in the cloud.
- Cloud security — Runtime protection for container and cloud workloads helps teams secure cloud deployments.
| Pros of Elastic Security | Cons of Elastic Security |
|---|---|
|
|
12. Grafana
(Free with paid options)
Grafana is an open-source, multi-platform analytics tool. It provides teams with interactive visualization capabilities such as dashboards, charts, and graphs to understand and query security-related data.
While Grafana itself is fully open source, Grafana Cloud is a commercial, fully managed observability stack with three pricing tiers:
- Cloud Free (with limited access)
- Cloud Pro ($29/month plus usage)
- Cloud Advanced ($299/month plus usage)
Key features:
- Security metric visualization — Grafana’s dashboards offer visibility into application and infrastructure security, displaying metrics like the number of security vulnerabilities, security scan results, and compliance status.
- Integration with security tools — Grafana’s range of integrations allows DevSecOps teams to centralize and visualize security data from these tools, helping them identify and respond to security incidents.
- Monitoring and alerting — Teams can configure Grafana to send alerts for specific events, such as breached thresholds or suspicious activity.
| Pros of Grafana | Cons of Grafana |
|---|---|
|
|
13. Splunk
(Paid)
Splunk is a platform for monitoring and analyzing machine-generated data. Its interface gives teams a space to report on and correlate security-related data in a container — making it easily searchable. Similar to Elastic Security, Splunk provides a dashboard for visualizing critical incidents.
Splunk offers various pricing models, including workload pricing, ingest pricing, entity pricing, and activity-based pricing. Exact pricing isn’t available online, so to learn more, contact Splunk.
Key features:
- Real-time monitoring and alerting — Splunk allows DevSecOps teams to monitor logs, events, and data from various sources in real-time. Teams can configure alerts and triggers based on predefined criteria or custom rules to notify them of anomalies.
- Security orchestration and automation — Splunk supports the automation and orchestration of security processes.
- SIEM capabilities — Splunk’s SIEM features provide a centralized platform for teams to collect, analyze, and correlate security-related data from different sources.
| Pros of Splunk | Cons of Splunk |
|---|---|
|
|
How to use n8n with DevSecOps tools
As you’ve seen, you can integrate various high-performing DevSecOps pipeline tools to make your applications and systems more secure.
Yet, while they work great independently in specific cases, sometimes they lack connectivity to sales, operations, finance, and other tech stacks. n8n extends these tools’ potential, seamlessly integrating them into whatever service you need.
n8n is a powerful yet user-friendly workflow automation tool for streamlining security processes. Along with native integrations (including all of the tools we’ve outlined) and hundreds of available workflow templates, n8n provides an intuitive drag-and-drop UI that lets teams build automated security workflows with ease. If your existing security tools lack native integration, you can add functionalities with JavaScript or Python using an iterative approach.
Let’s explore how teams can use these tools for four security functions: threat modeling, monitoring, alerting, and visualization.
Threat modeling tools
The following tools have powerful threat-modeling capabilities:
Effective threat modeling tools help organizations identify security threats, uncover patterns in vulnerabilities, evaluate threat severity, and form strategies for remediation and prevention.
Thanks to their integration with n8n, these tools can seamlessly fit into the DevSecOps pipeline. For example, the MISP node in n8n facilitates automated management of attributes, feeds, events, and warning lists. Teams can use this n8n integration to automate work in MISP, helping events stay up-to-date.
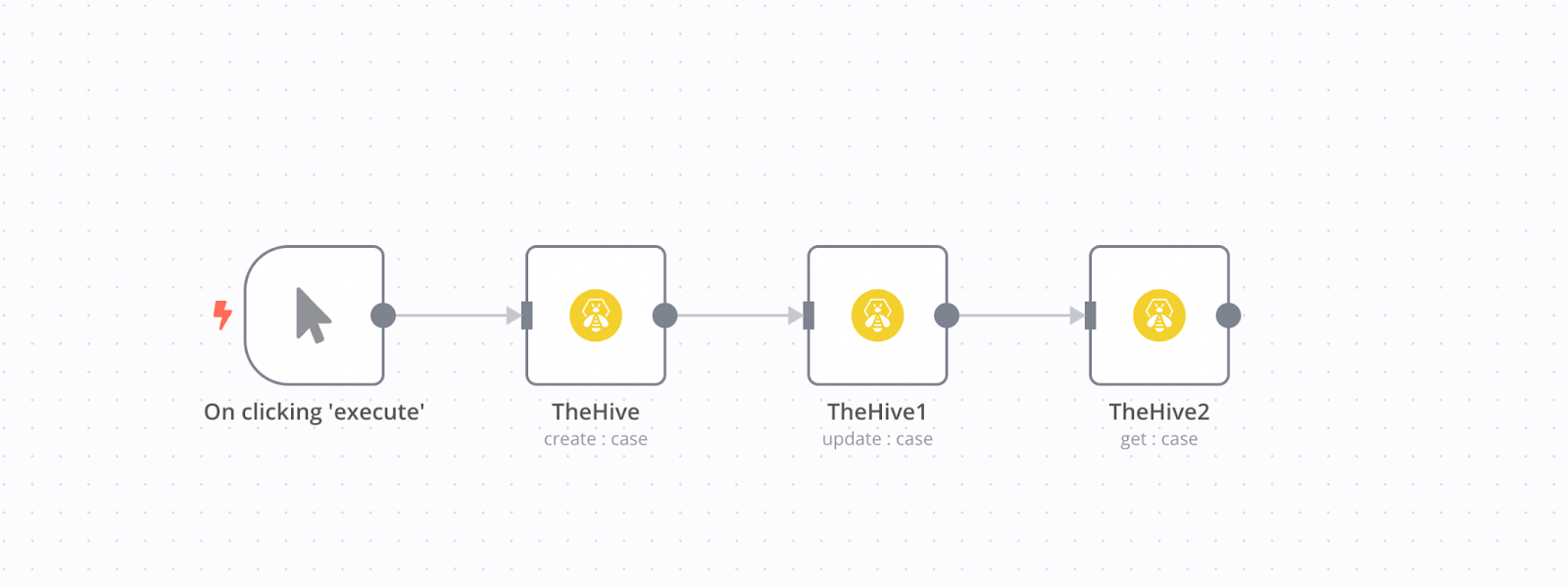
Similarly, TheHive node allows teams to create workflows for handling cases, providing valuable insights into past and current security incidents.
n8n’s Cortex node also offers analytic functions, generating reports on different job functions.
Monitoring tools
Monitoring tools help DevSecOps teams track potential security incidents and vulnerabilities automatically. They also enable triaging and threat escalation to ensure threats receive attention according to their severity.
The following tools excel in monitoring:
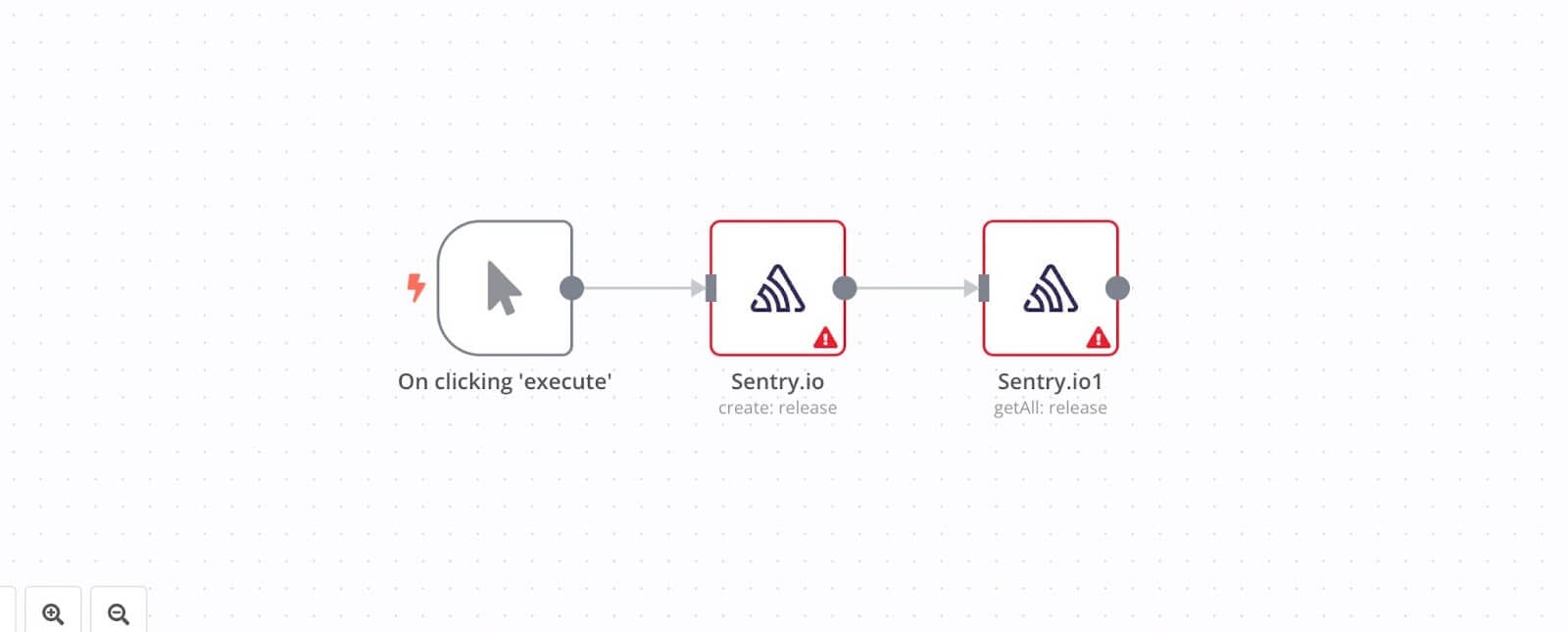
The Sentry.io node aids in identifying and managing information about release events and security issues. DevSecOps teams can use n8n to create workflows that fetch releases and use Sentry’s visual tracing capabilities to monitor technical issues.
The ServiceNow node in n8n provides a similar function, helping teams monitor incident resolution progress. SecurityScorecard’s reports seamlessly integrate into DevSecOps workflows.
Microsoft users can leverage the Graph security node to monitor security activity across their Microsoft security ecosystem.
Alerting tools
Alerting tools inform you of security vulnerabilities the moment they arise — a non-negotiable requirement in DevSecOps. Teams can also use these tools to track the metadata of different jobs, helping them pinpoint unusual activity.
These tools offer exceptional alerting capabilities:
Thanks to their native integration with n8n, these tools make it simple for DevSecOps teams to automate alerting within their security workflows.
For example, the SIGNL4 node allows teams to send and resolve alerts. Teams can create an n8n workflow that stores alerts in a database like Notion or create a workflow that sends alerts when file changes occur.
With the Rundeck node, teams can configure workflows to execute jobs and automatically report back with the metadata of a specific job.
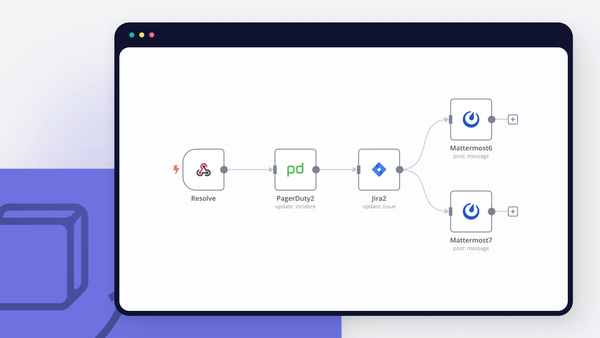
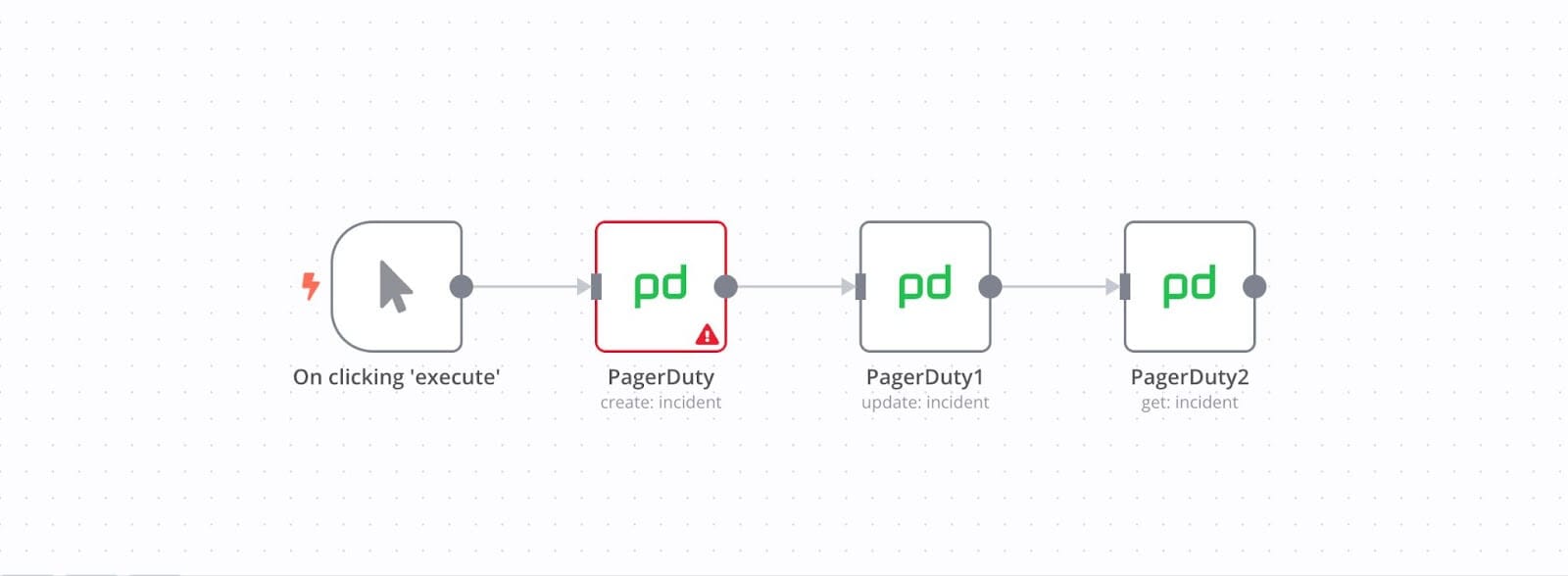
PagerDuty’s node enables teams to manage incidents, leave incident notes, and identify abnormalities in log entries from within their n8n workflow. For example, teams can configure their n8n workflow so that PagerDuty automatically creates and updates incidents.
Visualization tools
Finally, there are visualization tools, which offer a straightforward, streamlined way of sharing security-related information.
These tools have the strongest visualization features:
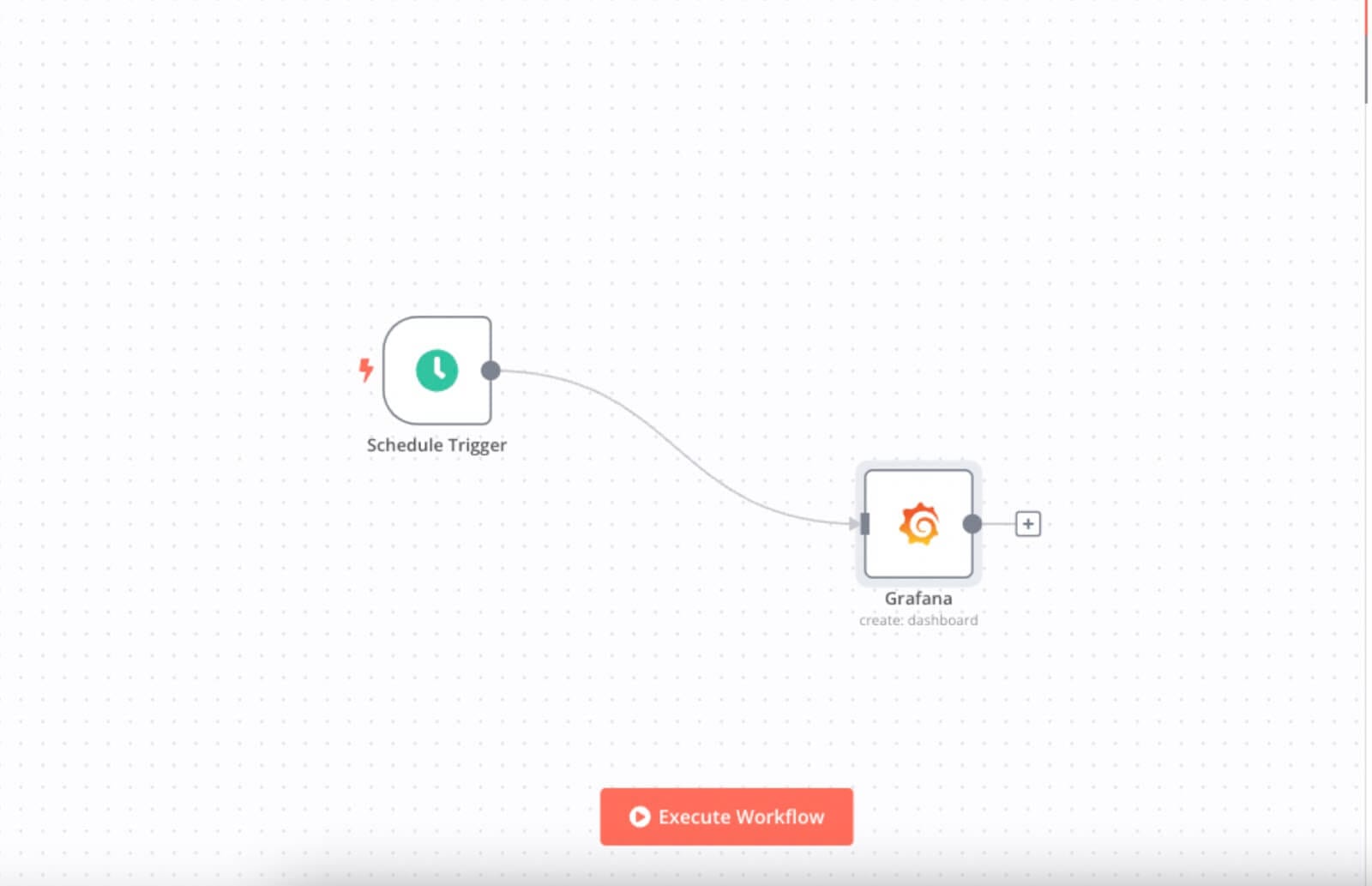
Using the Elastic Security node, DevSecOps teams can create supplementary Elastic Security dashboards that present security alerts visually. Similarly, teams can configure n8n’s Grafana node to automatically create visual dashboards by executing a workflow.
With the Splunk node integrated into n8n, teams can trigger automated visual reports of critical security incidents and resolution progress.
DevSecOps tools FAQ
We’ve covered a lot of ground, so let’s go back to basics. If you still have questions about these DevSecOps platforms and their potential, the following FAQs might have the answer.
What is DevSecOps, and what are DevSecOps tools?
DevSecOps tools are software solutions designed to integrate security practices and measures into the DevOps pipeline. They help organizations address security vulnerabilities and threats early — and throughout the development lifecycle.
What are the differences between DevOps tools and DevSecOps tools?
DevOps tools help automate and streamline the software development and deployment processes, while DevSecOps tools integrate security practices into the DevOps pipeline. Tools for DevSecOps typically include security scanning, vulnerability assessment, and compliance monitoring components, alongside the standard DevOps toolset.
What role in the pipeline does DevSecOps software play?
DevSecOps pipeline tools integrate security practices into the software development process. They’re built into the DevSecOps pipeline, ensuring the consistent maintenance and active pursuit of security at every stage of the workflow.
How do you implement DevSecOps tools?
Implementing DevSecOps tools involves integrating security practices and tools into the DevOps pipeline. This can include performing automated security testing, vulnerability scanning, compliance checks, and other security-related functions discussed above.
What’s next?
As your infrastructure grows, monitoring every facet becomes more challenging for DevSecOps teams. Making updates, tracking incidents that span the infrastructure, and effectively analyzing them can grow challenging — making DevSecOps automation tools essential.
n8n has an eye for automation.
By automating DevSecOps workflows with n8n, you can stay proactive in maintaining security and ensuring system safety, service availability, and customer satisfaction. In addition to more than 350 integrations, you can connect Cisco Secure Endpoint, Okta, Crowdstrike, Microsoft Entra ID, QRadar, Carbon Black, AlienVault, and many more DevSecOps essentials.
Learn how to set up a no-code CI/CD pipeline with GitHub and Travis CI, triggering a build with any push or pull request. Or, learn how to automate every step of an incident response workflow, including making tickets, communicating, and managing the overall process.